SEE AND ACT LIKE A HACKER
Cybersecurity for AI Velocity
AI ships code faster. Attackers exploit faster using AI. Periodic scans and annual pentests create false confidence in a real time threat world
WHY NOW
Security Broke When AI Accelerated Everything
AI-Driven Development
Code, cloud, and integrations change daily—security debt compounds instantly.
AI-Driven Attacks
Attackers automate recon, exploit chaining, and weaponization in hours.
Broken Security Models
Point-in-time scans and checklist pentests create false confidence in environments that never stand still.
Innovative Startup of the Year 2025
Recognized as Innovative Startup of the Year 2025 at ApexCXOs, Dubai trusted by CISOs who believe in our vision.
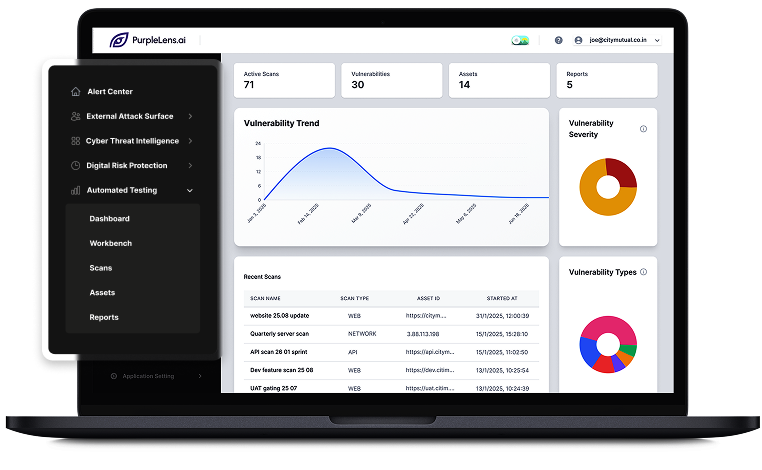
What we do
From Guesswork to Proof of Exploitability
PurpleLens.ai continuously validates what can actually be breached across your external attack surface right now.
Attack Surface Discovery – Continuously maps exposed assets as they appear
Threat Intelligence Led Testing – Tests against live attacker techniques
Evidence-Based Validation – Proves exploitable paths, not theoretical risk
How It WorkS
Continuous Testing, Not One-Time Assessments
Discover - Automatically identify internet-facing assets and shadow infrastructure
Detect - Detect new risks as your business changes
Test - Continuously simulate real-world attack paths using AI-driven testing
Fix & Prioritize - Validate exploitable risk with evidence and clear remediation guidance
Why PurpleLens.ai Wins
Built for AI-Speed Environments
Legacy Security Approach
Periodic scanners
Multiple tools
The PurpleLens.ai Advantage
Continuous attack validation
Proof of exploitability
Built for lean teams

Business IMPACT
Measurable Risk Reduction at AI Speed
1
Reduced Breach Probability
Continuous validation closes gaps before attackers exploit them
2
Faster Risk Response
Prioritized, evidence backed remediation
3
Lower Security Complexity
One platform instead of fragmented tools
4
Defensible Decisions
Security backed by attack evidence not checklists
Test Security at Attacker Speed
See what can be breached in your environment before attackers do.